Investigation Reveals Student Selling Access To Vulnerable Sites On Telegram And Using Beima Malware In Global Cybersecurity Attacks.
The increasing exploitation of vulnerable sites by cybercriminals has gained a new chapter.
After researchers from the security firm Cyderes identified, in Bangladesh, a university student who has been operating a sales scheme for access through a hacker Telegram channel for about a year and a half.
The discovery, made in direct conversations with the person responsible, details what is being sold (access to hacked pages), who conducts the operation (a student whose identity has not been revealed), when the activity began (18 months ago), where it occurs (mainly in Asia).
-
A “silent skill” is allowing Brazilians to earn up to R$ 22,000 per month without a degree and become indispensable for companies that rely on millions of data to survive.

-
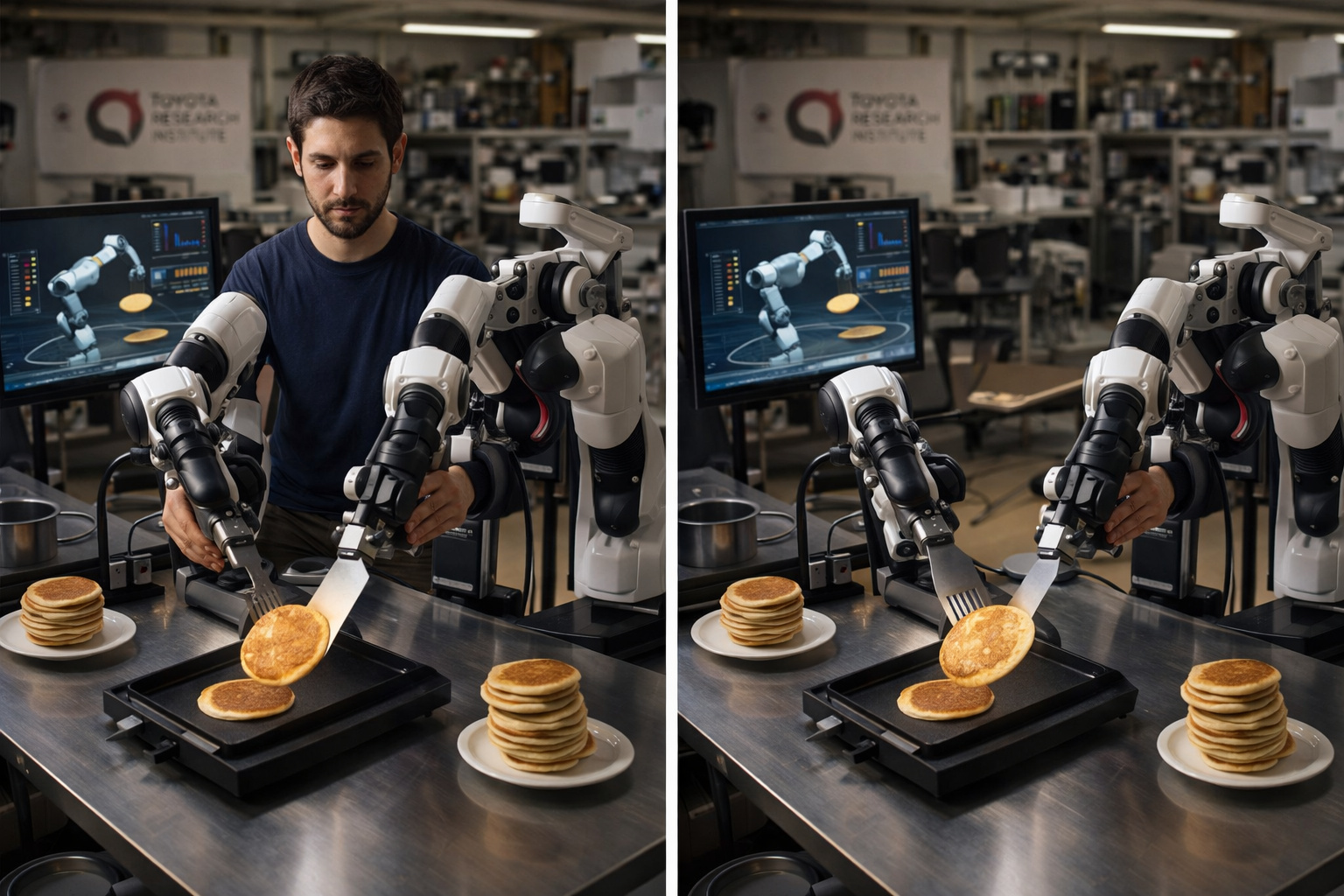
Researchers at the Toyota Research Institute found that if a human uses robotic arms to flip a pancake 300 times in an afternoon, the robot learns to do it on its own the next morning, and this is currently the most promising method to solve the biggest bottleneck in modern robotics.
-
Goodbye iron: a common item in households is starting to lose space to technology that smooths clothes in minutes without an ironing board and with less energy consumption.

-
Antarctica reveals an unusual clue high in the Hudson Mountains, and what appeared to be just an isolated rock began to expose a secret hidden under the ice for ages.

how the attacks are executed (exploiting faulty configurations and poorly protected panels) and why the university student claims to do this (to fund his studies and seek practical experience in offensive security).
Right from the first contact, Cyderes analysts realized that the scheme had expanded well beyond small invasions.
Underground Market Moves Access Starting At US$ 3
According to Cyderes, the university student offers full access to vulnerable sites at extremely low prices.
Small pages cost between US$ 3 and US$ 4, values that range between R$ 16 and R$ 21. However, when it comes to more valuable domains such as renowned universities, legal institutions, courts, governments, and military organizations, the price rises to around US$ 200 (approximately R$ 1,060).
Still, the impact of his actions is significant, as the access sold can serve both for fraud and for international espionage activities.
Telegram Hacker Exposes Global Network Of Malicious Operators
The investigation revealed that the university student is not alone. From Telegram, experts mapped an extensive network of criminals offering everything from access to poorly configured sites to complete codes to hack systems and steal information.
Although many participants are students, there are also technology researchers and professionals from various fields looking for “extra income” from this practice.
Additionally, the operator from Bangladesh primarily exploits WordPress sites with known vulnerabilities and pages managed via cPanel without proper protections.
In some cases, the problem is as basic as the default administrator password being left active, while in others there is exposure of .env files, containing credentials and API keys.
More Than 5,200 Compromised Sites In Various Countries
The scale of the operation is impressive. The student claims to sell access to more than 5,200 sites of organizations around the world.
Asia leads the occurrences, accounting for 72% of the total, particularly in Indonesia and India. However, victims also exist in Brazil, Libya, and the United States.
Almost half of the hacked pages belong to the educational sector, while about 25% are linked to government entities, which increases the risk of using the data for strategic purposes.
Buyers follow the same geographic pattern, being mainly Chinese, Indonesians, and Malaysians.
Beima Malware: Stealthy And Practically Undetectable Tool
In the 80 cases analyzed by Cyderes, the use of Beima malware stands out.
The command and control (C2) tool has stealth behavior, operates via JSON, uses embedded RSA keys, and hides in common API calls, making detection by conventional systems difficult.
The Beima also alters the insertion date of malicious files to 12 hours before the attack, deceiving solutions that identify recent changes. According to researchers:
“So far, Cyderes considers Beima completely undetectable by modern security tools.”
Another critical detail is that the code only executes malicious functions in specific contexts, making it difficult to create effective signatures for pattern-based antivirus solutions.
Alerts Are Increasing, Along With The Need To Strengthen Cybersecurity
The case underscores the advancement of digital crime driven by anonymous communication platforms and the underground commerce of access.
The combination of a hacker Telegram, vulnerable sites, and highly stealthy malware, such as Beima, creates a growing risk scenario for companies, governments, and citizens.
Experts emphasize that prevention remains the primary weapon: constant system updates, strong passwords, proper management of sensitive files, and log monitoring.

 Portuguese
Portuguese  English
English  Spanish
Spanish 




Seja o primeiro a reagir!