Script of the Scam Exposed by Filipe Deschamps Shows Use of Leaked Data, “Fake CNPJ”, Sudden Switch to CPF and AI Techniques to Clone Voice and Images.
A case reported by Filipe Deschamps lays bare the new manual of digital fraud: with leaked data, criminals create a fake profile on WhatsApp, call your mother “mom”, use a public photo, and try to rush a Pix transfer. The step-by-step includes “fake CNPJ” and, if there is suspicion, sudden switch to CPF, always with self-destructing messages and plausible stories.
In the video, Deschamps gathers an ethical hacker (Penegui), lawyer Luís Augusto Durso, and creator Programador BR to demonstrate how clandestine leaked data panels reveal relatives, addresses, and profiles, and how AI already allows forging photo, audio, and even video.
The goal is singular: to request Pix. “This will worsen”, the group warns, by showing voice cloning with mere 30 seconds of samples.
-
A forgotten cord on the floor of a basement in Vienna leads a plumber to a box containing 30 kilograms of gold with Mozart’s face, hidden before World War II. The treasure, worth 2.3 million euros, was just centimeters away from a worker who ignored the sign a day earlier.

-
A couple buys an old chalet, breaks the kitchen floor for renovation, and finds over a thousand coins of gold and silver hidden since the English Civil War over 4 centuries ago.

-
Rigid bags with their days numbered: new trend prioritizes comfort in 2026.

-
YouTuber creates an excavator equipped with a giant 4.5-meter sword to challenge his brother to a rematch, and the invention quickly goes viral on social media.

How the Scam Starts: Fabricated Proximity
The contact arrives via WhatsApp with a “Hi, mom” and a believable photo taken from public networks. Details give it away: area code out of family standard, chat set to delete messages in 24h and profile picture different from the one you know.
Even so, the emotional appeal speaks volumes and it’s here that scammers insist on urgency (“I need to pay now”) to avoid verifications.
In the case narrated by Filipe Deschamps, the mother noticed the strange area code, but the scammer kept up the pressure. Urgency is a central strategy: it lowers her critical sense, blocks verification by call, and creates the perfect atmosphere for Pix.
The Money Script: From “Fake CNPJ” to “Last-Minute CPF”
The sequence is almost always this: first, a “clean” CNPJ is sent to receive the Pix. If the victim hesitates or asks for time, the account is deleted and an “alternative” CPF appears.
In the reported case, the criminal even deleted the message with the CNPJ and reappeared with CPF key, trying to rush past the doubt: “just do it and send me the proof”.
Why change accounts? Because they quickly burn the keys orbiting in “fake company” schemes and test options until the operation goes through without a block.
Self-destructing messages and truncated justifications (“didn’t you hear the audio?”) help to erase tracks and confuse those trying to preserve evidence.
Leaked Data Panels: Why They Know Who Your Mother Is
According to ethical hacker Penegui, criminals use panels assembled from major leaks and, many times, data stolen from within agencies and companies.
The result is a parallel database that crosses public health system, driver’s license/transport agency, tax revenue, e-commerce, and social networks. This is how the scammer “knows” who the mother, father, spouse, or child is.
These panels mix old leaks and recent internal data, delivering updated information enough to seem intimate.
This contextual power gives credibility to the narratives and breaks defenses of those who are under emotional impact.
AI Boosting Fraud: Photo, Voice, and Video
In Deschamps’ demonstration, fake images were generated with free AIs from a public photo — even setting up an “accident” in the victim’s city.
Even with watermarks and fake license plates, relatives reacted to emotional shock before analyzing the details. When emotion takes the wheel, logic hits the brakes.
In the audio, Programador BR shows voice cloning with 30 seconds of recording, enough for Pix requests “in your voice”.
And video models already allow realistic face swapping. Central message from the trio: “With leaked data and AI, scams will become more sophisticated, not slow down.”
What to Do in the Moment: Anti-Panic Protocol
1) Don’t Interact. Block. The lawyer Luís Augusto Durso gives clear guidance: avoid extracting ‘more data’ from the scammer. Prolonged interaction opens breaches for malicious links and retaliation using your own leaked data.
2) Confirm via Another Channel. Never pay without calling (video/call) the supposed requester from a number already saved. Short and objective phrases help: “I’ll call you now on the old number”. Scams can’t withstand live voices.
3) Save Evidence Without Clicking. Screenshots of conversations and Pix keys (CNPJ/CPF) serve as inputs for legal steps. Don’t open links and don’t download attachments.
4) Train the Family. Establish an emergency password (“signal word”), agree on the “always call first” rule and set alerts in the family group (strange area code = be suspicious; urgent request = stop, breathe, check). Recurring education is the best antivirus.
If You Already Fell: Legal and Banking Paths
1) Police Report (Online). Report immediately the BO with all evidence (number, screenshots, Pix keys). Repeated patterns help police connect cases and notify banks.
2) Notify the Bank and the Pix MED. With the BO in hand, notify your bank and the destination bank requesting the Special Mechanism for Refund. The sooner, the better the chances of blocking funds.
3) Escalated? Go Judicial. If the reimbursement is denied, legal actions can seek fund recovery and accountability. Informing keys and accounts used in the scam helps to dismantle recurring structures.
Shielding Checklist: Minimum Viable Domestic Security
Keep WhatsApp with two-step verification and session alerts. Hide sensitive data on networks (birth date, explicit kinship, family phone numbers). Beware of “urgency” + “new number” + “Pix”: this is the tripod of the scam.
Adopt a signal phrase for emergencies; agree that no one sends Pix without a prior call; and standardize confirmation questions that AI and data panels can’t answer (things AI can’t answer – family memories, internal nicknames, non-public information). Repetition creates reflex: stop, confirm, only then act.
The explosion of leaked data and AI tools has changed the rules of the game: the scam now knows your family and speaks like you. In light of this, what protocol will your house adopt? Do you already have a signal word?
Who in your circle would be most vulnerable to an “urgent Pix request” with cloned audio? Share in the comments how you train your parents and grandparents, what situations you have already faced, and which measures worked — your account can shield other families.

 Portuguese
Portuguese  English
English  Spanish
Spanish 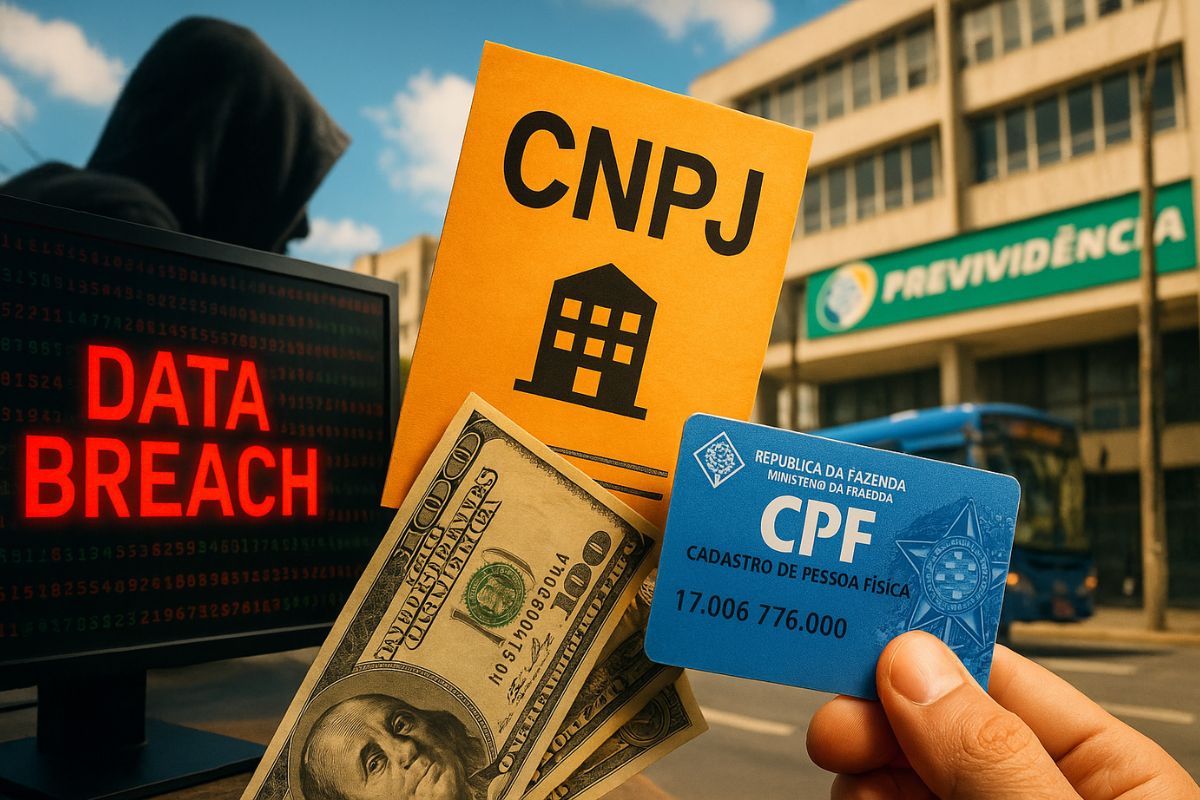






-

2 pessoas reagiram a isso.