Apple decided to enhance its rewards program for those who discover vulnerabilities in its products. This initiative, aimed at experts and enthusiasts in the field of digital security, now offers the largest payouts in the company’s history — and promises to attract a new wave of “bug hunters” from around the globe.
The program, known as Apple Security Bounty, has been completely revamped. Starting in November 2025, anyone who finds serious vulnerabilities in the brand’s systems or devices can receive up to US$ 2 million (around R$ 10.8 million) per report — double the previous maximum amount. This reward is reserved for cases where the researcher can demonstrate vulnerabilities with potential similar to advanced spyware attacks that exploit gaps without the victim’s knowledge or consent.
New Bonuses and Vulnerability Categories
In addition to the new payment ceiling, Apple has added extra layers of incentive. Bugs that can bypass the Isolation Mode — a feature aimed at protecting journalists, activists, and public figures — will have additional bonuses. The same applies to vulnerabilities detected in the brand’s Beta versions of operating systems prior to official release.
-
In China, a single person with artificial intelligence tools can already do the work of 50 to 100 employees: the new five-year plan bets on the one-person company model, and Suzhou is the laboratory for this revolution.

-
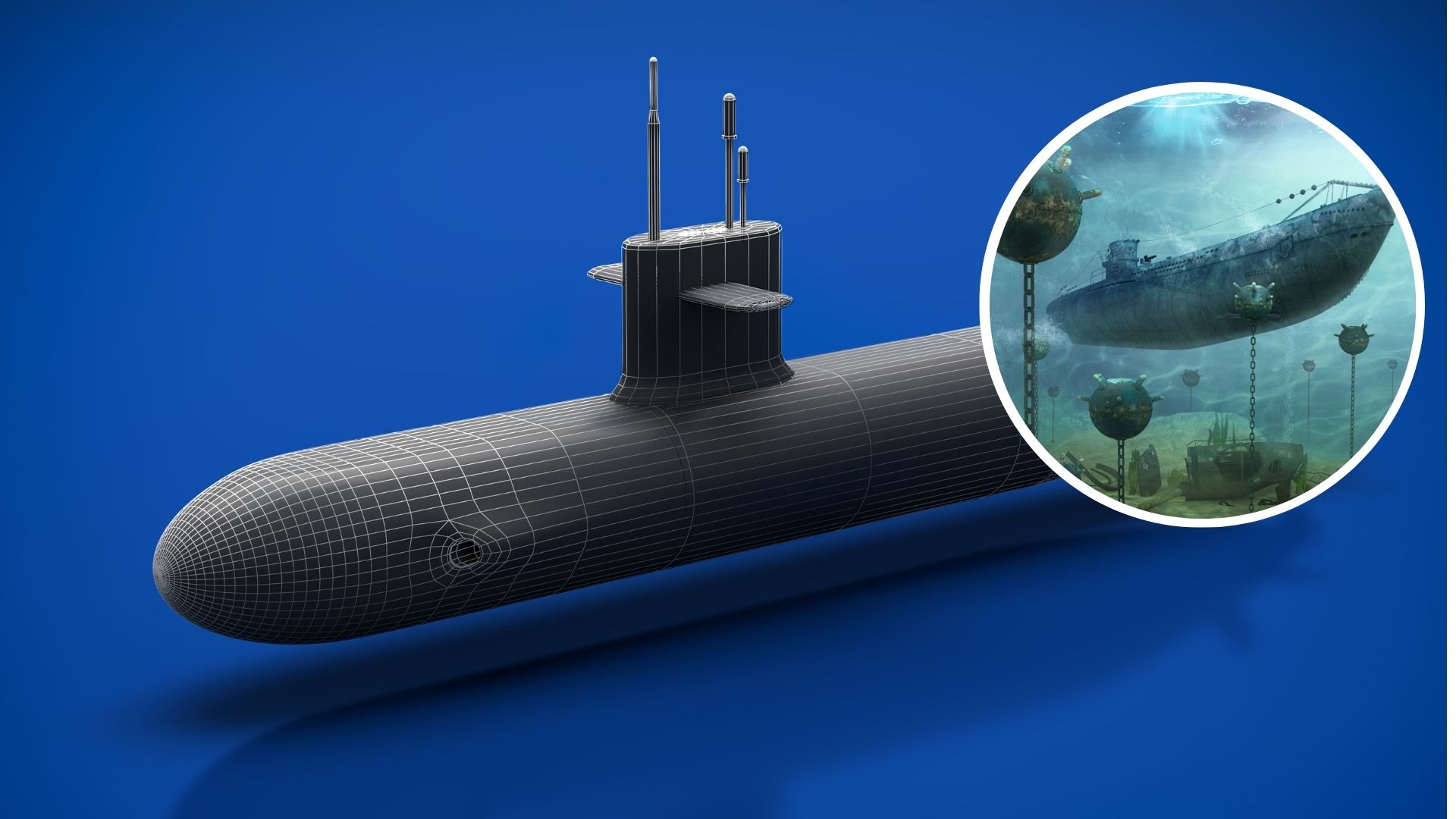
The USA accelerates the production of sensors launched into the ocean to hunt quieter submarines, and the new system promises to detect targets at greater distances in rough seas, shallow waters, and noisy areas, changing the game of anti-submarine warfare.
-
Science has discovered that white hair is not a sign of the body’s failure but rather a defense mechanism that sacrifices the color of the strands to protect the root against something much more serious.

-
Scientists believed that this marsupial had disappeared 6,000 years ago, but an expedition found two living specimens in a remote forest in New Guinea with a finger that no other animal on the planet possesses.

With the sum of rewards and bonuses, a single participant can receive up to US$ 5 million (approximately R$ 27 million) if the discovery meets all the established criteria. According to the company, the focus is to direct efforts toward security flaws with the potential for large-scale espionage, putting aside isolated errors in apps or individual components. The goal is to prevent incidents similar to the case of the Pegasus spyware, which has challenged even the world’s largest technology companies for years.

Focus on New Areas and Technologies
Among the new categories included are unprecedented vulnerabilities in services such as iCloud and in Gatekeeper, a mechanism that protects Macs from unauthorized software execution. The company also confirmed that the iPhone 17, expected next year, will be part of the program, with special attention to vulnerabilities specific to the new generation of phones.
To simplify the submission and analysis of findings, Apple created the Target Flags system, a kind of “digital flagger” that classifies the type of identified flaw. Each validated report receives a flag and a corresponding icon, which speeds up the internal triage and prioritization process for payments.
One of the Largest Reward Programs in the World
With these changes, the company strengthens its position as one of the most engaged in the global bug bounty community. Since the public launch of the program in 2020, over US$ 35 million has been distributed to more than 800 security researchers. Several experts have received US$ 500 thousand in individual awards for reports deemed critical.
Those interested in participating in the new phase of the Apple Security Bounty can access the company’s security page to understand the rules, vulnerability categories, and eligibility criteria.
The new guidelines come into effect in November 2025, and it is expected that the number of participants will grow exponentially — after all, who wouldn’t want to earn millions for finding a flaw before hackers do?

 Portuguese
Portuguese  English
English  Spanish
Spanish 






-

-

3 pessoas reagiram a isso.