Subtle changes in phone performance can indicate invisible digital security risks, requiring immediate attention to prevent data loss, account invasions, and financial damages resulting from silent malicious software actions.
Sudden changes in phone performance can indicate security flaws, malware presence, or unauthorized account access, especially when accompanied by overheating, unusual data consumption, and unexpected changes in overall system behavior.
While a single sign may not be enough to confirm an invasion, the combination of these indications requires immediate attention and careful analysis by the user, especially given the increase in attacks targeting mobile devices in Brazil.
According to guidelines from CERT.br, linked to NIC.br, cell phones and tablets should be treated as sensitive devices, as they contain personal messages, photos, access credentials, banking data, and various information that can be exploited in fraud.
-
For the first time in history, a submarine cable will descend to four thousand meters deep under the ice of the North Pole to ensure that the internet between Europe and Asia no longer depends on conflict zones in the Middle East.
-
A British company has installed in the middle of the ocean the world’s first floating platform that generates electricity 24 hours a day from the temperature difference between the surface and the depths of the Atlantic, without relying on wind or sun.
-
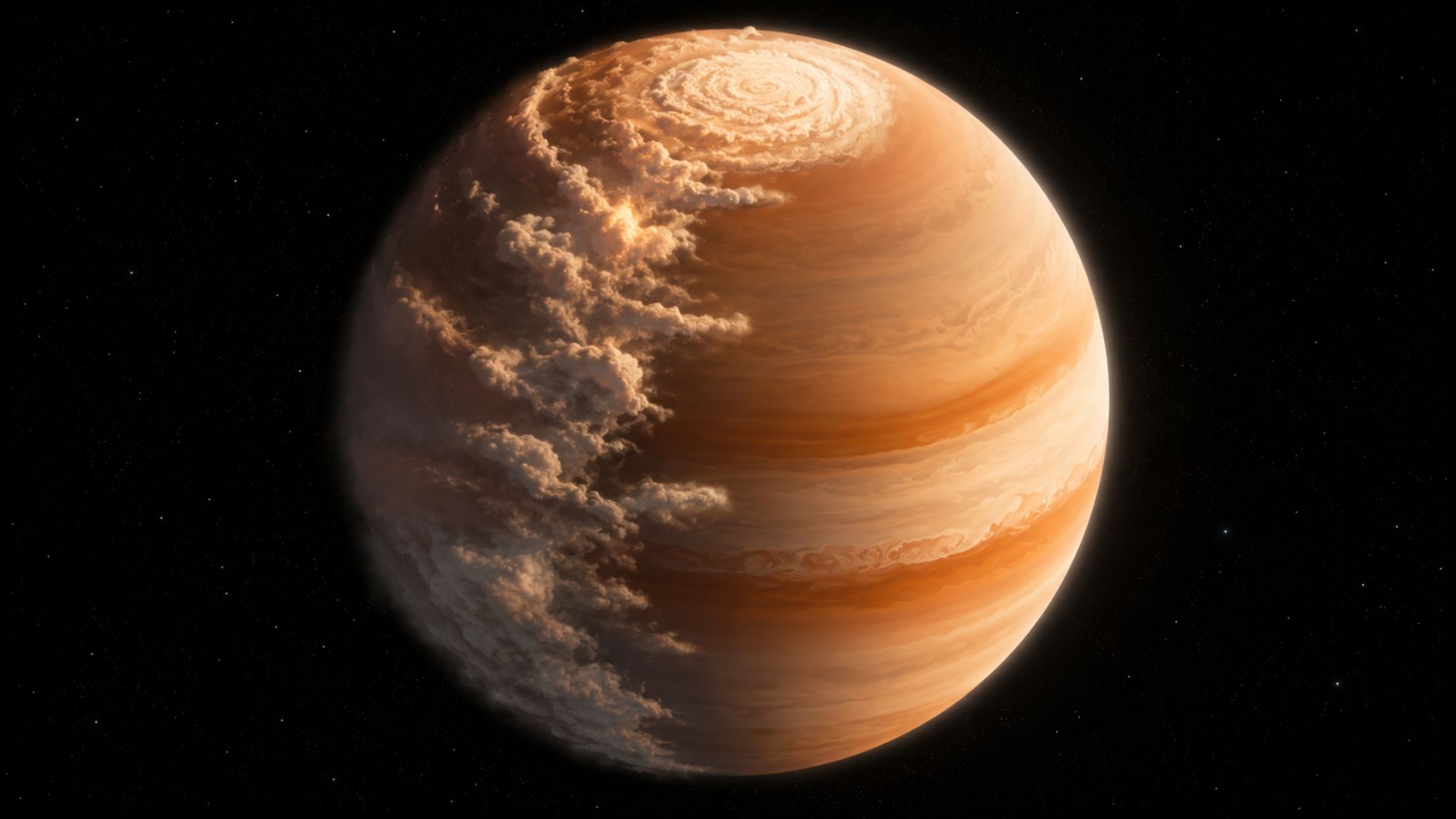
The James Webb telescope spotted a planet 700 light-years from Earth with mornings full of sand clouds and nights with clear skies, the temperature difference between the two hemispheres reaches an impressive 170 degrees.
-
A former Hong Kong police officer has just become the first astronaut from her city to go to space. She embarked on the Shenzhou-23 mission alongside two other colleagues who will face muscle atrophy, radiation, and prolonged fatigue in orbit.
In this context, the alert gains strength because the smartphone has come to centralize much of daily digital life, bringing together financial applications, social networks, authentication services, and personal communications in a single environment highly targeted by criminals.
Signs of a Hacked Phone and Performance Changes
Among the first noticeable signs, changes in the physical functioning of the device often draw attention, especially when the device exhibits abnormal heating, significant battery drain, or a sudden drop in performance without apparent reason.
In these situations, there is a possibility that malicious software is operating in the background, continuously consuming resources to collect information or send data to external servers without the user immediately noticing.
On the other hand, it is important to consider common causes for this behavior, such as battery wear, an excessive number of installed applications, failures in recent updates, or prolonged use in environments with high temperatures.
Thus, isolated analysis of this symptom can lead to mistaken interpretations, making it essential to cross-reference this indication with other signs before concluding that the device is compromised.
Another relevant factor involves abnormal mobile internet consumption, which may indicate the presence of spyware or malicious programs responsible for constantly transmitting information out of the device.
Even without intensive use of applications that require a connection, such as video streaming or file downloads, an unexpected increase in data traffic should be considered a relevant alert.
Furthermore, persistent slowness also deserves attention, especially when the system exhibits frequent freezes, takes a long time to open applications, or overheats during simple daily tasks.
Strange Phone Behaviors That Indicate Invasion
Unexpected changes in system behavior represent another important group of signs that may indicate device compromise, especially when they occur without any direct user action.
Among these indications, spontaneous reboots, constant appearance of pop-up windows, changes in application permissions, and the presence of unknown programs installed on the device stand out.
In parallel, it becomes essential to check the activity of accounts linked to the phone, as suspicious movements may indicate that unauthorized access has gone beyond the device and reached personal credentials.
Sending unrecognized emails, unknown messages in chat applications, and login attempts from unusual locations are examples that reinforce the need for immediate investigation.
For Android devices, it is recommended to check Play Protect, review permissions granted to applications, verify security updates, and identify installations made outside the official store.
For iPhone devices, attention should be directed to configuration profiles, devices associated with the Apple ID, and permissions granted to applications with access to sensitive data.
What to do if you suspect a phone invasion
Given consistent suspicions, the first recommended action is to disconnect the device from potentially compromised networks and avoid accessing sensitive services, such as banking applications, emails, and social media.
Next, it is essential to change important passwords using another trusted device, prioritizing email accounts, financial services, and platforms that concentrate a larger volume of personal information.
As an additional layer of protection, two-factor authentication should be enabled whenever possible, prioritizing methods that do not rely exclusively on SMS.
Solutions such as authenticator apps, physical security keys, or passkeys offer greater resistance to scams involving SIM card cloning or message interception.
Subsequently, it is recommended to remove suspicious applications, review granted permissions, and ensure that the operating system is properly updated with the latest security patches.
While security applications can assist with verification, they do not replace basic protection practices such as using strong passwords, being cautious with downloads, and exclusively using official app stores.
When to hard reset your phone
In more critical scenarios, where signs persist or there are clear indications of compromise, a factory reset, known as a hard reset, may be necessary to completely eliminate potential threats.
This procedure removes all data stored on the device, including applications, settings, and any malicious code active in the system.
Before starting the process, it is essential to back up only reliable files, such as photos, contacts, and personal documents, avoiding automatically restoring applications that may be related to the problem.
After the reset, the recommendation is to manually reinstall only essential applications, ensuring greater control over what is used on the device again.
Additionally, it is necessary to change passwords again, end old sessions, and remove unknown accesses linked to previously used accounts.
How to prevent invasions and protect data on your phone
Prevention remains the main strategy to reduce risks, starting with the constant maintenance of the operating system and applications always updated.
Security patches are responsible for closing vulnerabilities exploited by criminals, significantly reducing the chance of infection by malicious software.
Another essential precaution involves avoiding access to suspicious links received via messages, as well as downloading files sent by unknown or unverified sources.
Scams based on social engineering remain among the most effective, exploiting user trust to induce actions that result in the installation of fake applications or the provision of credentials.
Additionally, periodically reviewing permissions granted to applications helps limit undue access to resources such as the microphone, camera, location, and contact list.
Finally, maintaining an updated backup ensures greater security in incident situations, allowing the recovery of important data without relying on emergency solutions that could further compromise the integrity of the information.

 Portuguese
Portuguese  English
English  Spanish
Spanish 







Be the first to react!